In addition to the acclaimed opinion in all corners of the Internet about hiding an IP address, there are many other details. All methods and means of anonymity pursue the goal of hiding the provider. Through which you can already get a physically accurate location of the user, having additional information about him (IP, browser fingerprints, logs of his activity in a certain network segment, etc.). As well as most of the methods and tools are aimed at maximum concealment / non-disclosure of this indirect information, which later can be asked from the provider of the desired user. One of the best ways to achieve anonymity is considered a proxy server, which you can find here Proxy-Seller.Com.
What are the ways to achieve anonymity?
If we talk about detached units of anonymization (there are still schemes in the form of a combination of one or another means of anonymity), we can distinguish the following:
- Proxy servers – there are different types, with their own characteristics. You can find them by reffering this link https://proxy-seller.com/german-proxy;
- VPN services – also work on different protocols offered by providers to choose from, see their differences and features below;
- SSH tunnels, originally created (and still function today) for other purposes, but also used for anonymization. By the principle of operation, they are quite similar to VPNs; therefore, in this topic, all conversations about VPN will imply them too but they have some differences;
- Dedicated servers – the most important advantage is that the problem of disclosing the query history of the node from which the actions were taken disappears (as can be the case with a VPN / SSH or proxy);
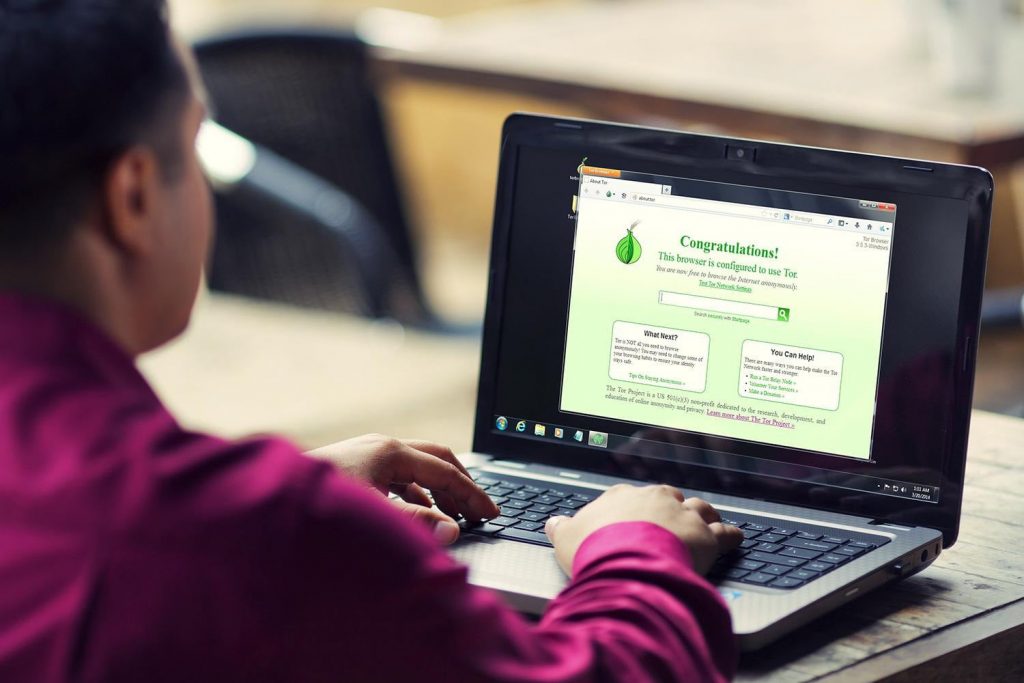
- Great and terrible Tor;
- I2P is an anonymous, decentralized network operating on top of the Internet, not using IP addressing;
- Other means – anonymous networks, anonymizers, etc. Due to the still insufficient popularity, they have not yet been studied (and therefore do not have a relative guarantee of reliability) by the community, but are quite promising;
What is worth hiding, or what is deanonymizing data and methods for obtaining them?
Immediately, we will note that all (basic at least) means and methods for hiding data in the list below will be covered in the remaining questions of this FAQ. I also want to draw attention to one interesting resource, which is devoted to the questions, what information we leave about ourselves on the network, going into different devices;
- IP-address, or the most popular identifier on the Internet. It makes it possible to find the provider of the user and find out the exact address through the same IP;
- IP DNS provider, which can be “lost” through a method called DNS leaks. It is important to note that this leakage can occur with HTTP / SOCKS4 (5 in some cases) + Tor! Therefore, we must be especially careful here;
- If most of the traffic goes to the Internet for a long time through one node, for example, the same Tor, then you can do so-called profiling – assign a certain activity to a certain alias, which can be done through other channels;
- Listening for traffic at the output node or Mitm-attacks (man in the middle);
- Simultaneous connection to anonymous and open channels may in some situations create troubles, for example, if the client disconnects, both channels will cease to function, and the server will be able to determine the desired address by matching the user disconnection time inaccurate deanonymization method);
- Deanonimizing activity in an anonymous session – using public services, especially those that already have information about this user;
- The MAC address that the WiFi point receives when it is connected to it (or it can be backed up by switches from one of the local networks through which Internet access was made);
- Information from browsers.

